Conference in media
Computer Society marks Russia’s 70th anniversary in computer science
ISP RAS signed an agreement with Taiwan research institute ITRI (in Russian)
ISP RAS will help RusBITech to improve the security of Astra Linux (in Russian)
RAS: the salaries of computer science investigators exceeded 200 000 rubles (in Russian)
About the Conference
The Ivannikov ISP RAS Open Conference is the annual event under which the Institute for system programming of the Russian Academy of Sciences (ISP RAS) arranges a number of conferences devoted to sectors of IT-industry in which it possesses a many years’ experience of fundamental researches conduction, innovative technologies development and implementation, together with partners, of certain projects on introduction the developed technologies in the industry.
The goal of this event is to provide support and development for the innovations generation and high-skilled system programming workers reproduction ecosystem, created in the ISP RAS as well as to create prerequisites for improving the level of using newest information technologies in activity of educational, scientific and research organizations and their further introduction in Russian industry. During The Ivannikov ISP RAS Open Conference sections reports on fundamental and applied researches as well as on issues related to new technologies introduction are made.
Acknowledged experts from national and foreign scientific and educational organizations, representatives of leading IT-companies and researchers whose studies have been professionally reviewed are invited to make reports.
Paticipation in the conference and publication of articles are free of charge. Travel and accommodation, as well as other expenses are to be paid by the participant.
Technologies of program analysis, modeling and transformation
The event is being held by joint initiative of the ISP RAS and is devoted to methods of optimization in compiler and code generation, static and dynamic program analysis, etc. Issues, examined under this event include, but are not limited to the following topics:
- Binary (executable) code reverse engineering.
- Program execution in controlled environment.
- Vulnerability search in executable code.
- Network traffic analysis.
- Compiler optimization and code generation.
- Program static and dynamic analysis.
- Program analysis and testing methods and tools.
Learn More
Management of Data and Information Systems
The event is intended for researchers specializing in data management and data analysis. We invite researchers working on methods and systems for storing and analyzing large volumes of text, graph, multimedia, scientific and other types of data. Issues addressed by the conference include, but are not limited to the following topics:
- Data mining and information extraction.
- Mathematical theory and methods of machine learning and artificial intelligence.
- Mathematical models of processes and phenomena of the real world.
- Computational linguistics, natural language text analysis and understanding.
- Complex networks analysis, including social, communication, biological networks, etc.
- Signal processing and image analysis.
- User-generated content analysis.
- Information retrieval, recommender systems.
- Ontologies and knowledge bases.
- Information systems and technologies.
- Scalable algorithms for data analysis.
- Data analysis applications.
- Data cleaning, heterogeneous data integration, data deduplication.
- Key technologies for private and hybrid clouds creation.
- High-performance computing and other services in clouds.
- Big data ecosystem.
- Distributed databases and Data/Web Mining technologies.
- Software platforms for internet of things.
- Dynamic load balancing in elastic clouds.
- Planning of task flow in cloud data processing centers.
- Power-saving cloud infrastructures.
Learn More
Technologies of distributed ledgers and blockchains
The event is being held by joint initiative of the ISP RAS and is devoted to technologies of blockchain and distributed ledgers. Issues to be considered during this event include, but are not limited to the following topics:
- Transactions and transaction validation. Consensus.
- Code execution on the ledger (smart contracts/chain code): languages, virtual machines, termination.
- Scalability and performance: storage and block construction.
- Network protocols for blockchain and DLT.
- Security and safety. New threats connected with DLT and blockchains.
- Trust in untrusted environments.
Learn More
Open source software in continuum mechanics problems solving
The event is intended for practical experience exchange between researchers, who use open applied packages for continuum mechanics problems solving. Issues being studied under this conference include but are not limited to the following subjects:
- Turbulent flows modeling.
- Solving adjoined thermal exchange problems.
- Applied hydrodynamics, gas dynamics and aerodynamics problems.
- Development of personal problem solvers and libraries.
- Scientific visualization and processing of numerical results.
- Education based on open packages issues.
Learn More
Thursday, 22 November
Registration. Welcome coffee (The Green Hall – The Foyer)
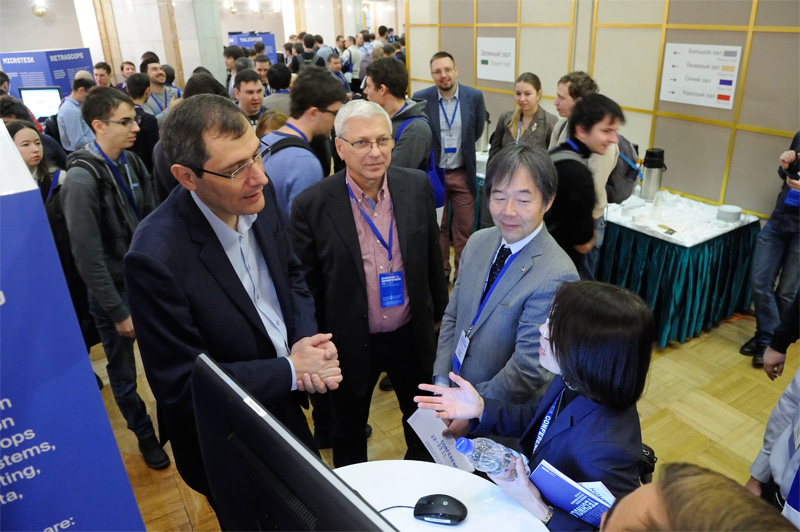
Participants represent Russian government, Russian academy of sciences, executives of research institutes, universities, leading Russian and international IT-companies, IEEE and IEEE Computer Society executives
Plenary session: "History of continuous innovation". Devoted to the 70th anniversary of Russia’s computer science.
Management of Data and Information Systems (The Beige Hall)
Tsolak Ghukasyan1, Garnik Davtyan1, Karen Avetisyan1, Ivan Andrianov2
1 System Programming Laboratory at Russian-Armenian University, 2 ISP RAS
"pioNER: Datasets and Baselines for Armenian Named Entity Recognition"
Learn moreDownload PDF
N. Lazarev1, O. Borisenko2
1 Lomonosov Moscow State University, 2 ISP RAS
"Implementing JSON operations for In-memory Data Grid as pass-through cache layer to RDBMS"
Download PDF
O. Borisenko 1, D. Badalyan 1
1 ISP RAS
"Evaluation of SQL benchmark for distributed in-memory Database Management Systems"
Download PDF
I. Alimova1, E. Tutubalina1
1 Kazan Federal University
"Entity-level classification of adverse drug reactions: a comparison of neural network models"
Learn moreDownload PDF
Coffee, tea
Andrei Tchernykh1, Rewer Canosa1, Jorge M. Cortés-Mendoza1, Raul Rivera-Rodriguez1, Jose Lozano Rizk1, Zhihui Du2, Arutyun Avetisyan3, Eduardo Concepción-Morales4
1 CICESE Research Center, 2 Tsinghua University, 3 ISP RAS, 4 UMET
"Energy consumption and quality of service optimization in containerized cloud computing"
Learn moreDownload PDF
Valentin Malykh1, Taras Khakhulin1
1 MIPT
"Noise Robustness in Aspect Extraction Task"
Learn moreDownload PDF
Kristina Pivovarova1, Irina Bolodurina1, Denis Parfenov1
1 Federal State Budgetary Educational Institution of Higher Education "Orenburg State University"
"Development and research of models of time mixed-frequency data on an example of the analysis of productivity of grain crops"
Learn moreDownload PDF
Suzanne Habashi1, Cherif Salama1, Ahmed H. Yousef1, Hossam Fahmy1
1 Ain Shams University
"Adaptive Diversifying Hyper-Heuristic Based Approach for Timetabling Problems"
Learn moreOpen source software in continuum mechanics problems solving (The Green Hall)
Matthias Banholzer1, Christoph Traxinger1, Michael Pfitzner1
1 Bundeswehr University, Munich, Germany
"Numerical investigation of phase separation effects under high-pressure, engine-like conditions"
Learn moreSergei Strijhak1, Arina Kryuchkova1, Konstantin Koshelev1
1 ISP RAS
"Computation of flow parameters in model wind farm based on wind measurement data"
Download PDF
Coffee, tea
Mikhail Levin1
1 ISP RAS
"Numerical Investigation of Two-Phase Flows Through Essentially Heterogeneous Porous Media by High-Order Quasi-Characteristics Scheme"
Download PDF
Igor Kulikov1, Igor Chernykh1, Dmitry Karavaev1, Viktor Protasov1, Aleksandr Serenko1, Vladimir Prigarin1, Ivan Ulyanichev1, Alexander Tutukov2
1 Institute of Computational Mathematics and Mathematical Geophysics SB RAS, 2 Institute of Astronomy RAS
"Using adaptive nested mesh code HydroBox3D for numerical simulation of Type Ia supernovae: merger of carbon-oxygen white dwarf stars, collapse, and non-central explosion"
Learn moreDownload PDF
Kirill Terekhov1, Igor Konshin1, Yuri Vassilevski1
1 Marchuk Institute of Numerical Mathematics of the RAS
"INMOST — a software platform for distributed mathematical modeling"
Learn moreDownload PDF
Mikhail Zaitsev1, Vasilij Goloviznin1, Sergey Karabasov2
1 NSI RAS, 2 Queen Mary University of London
"Implementation of CABARET method for polyhedral cells in OpenFOAM"
Download PDF
Artem Kuvshinnikov1, Alexander Bondarev1
1 Keldysh Institute of Applied Mathematics
"Comparative estimation of QGDFoam solver accuracy for inviscid flow around a cone"
Learn moreDownload PDF
Technologies of program analysis, modeling and transformation (The Blue Hall)
Vladislav Ivanishin1, Evgeny Kudryashov1, Alexander Monakov1, Dmitry Melnik1, Jehyung Lee2
1 ISP RAS, 2 Samsung Electronics, Software Center
"Pruning ELF: Size Optimization of Dynamic Shared Objects at Post-link Time"
Learn moreDownload PDF
Irina Dudina1, Nikita Malyshev1
1 ISP RAS
"An approach to the C string analysis for buffer overflow detection"
Learn moreDownload PDF
Vitaly Cheptsov1, Alexey Khoroshilov1
1 ISP RAS
"Dynamic Analysis of ARINC-653 RTOS with LLVM"
Learn moreDownload PDF
Grigoriy Volkov1, Mikhail Mandrykin2, Denis Efremov1
1 NRU HSE, 2 ISP RAS
"Lemma Functions for Frama-C: C Programs as Proofs"
Learn moreDownload PDF
Coffee, tea
E.M. Lavrischeva1
1 ISP RAS
"Informatics and Computer-70. Analysis and development aspects"
Learn moreDownload PDF
A.V. Kozachok1
1 Academy of the Federal Guard Service
"TLA + based access control model specification"
Download PDF
Nikolay Shilov1, Igor Anureev2, Evgeny Bodin2, Dmitry Kondratyev2, Alexei Promsky2
1 Innopolis University, 2 A.P. Ershov Institute of Informatics Systems
"Towards platform-independent specification and verification of the standard mathematical functions"
Download PDF
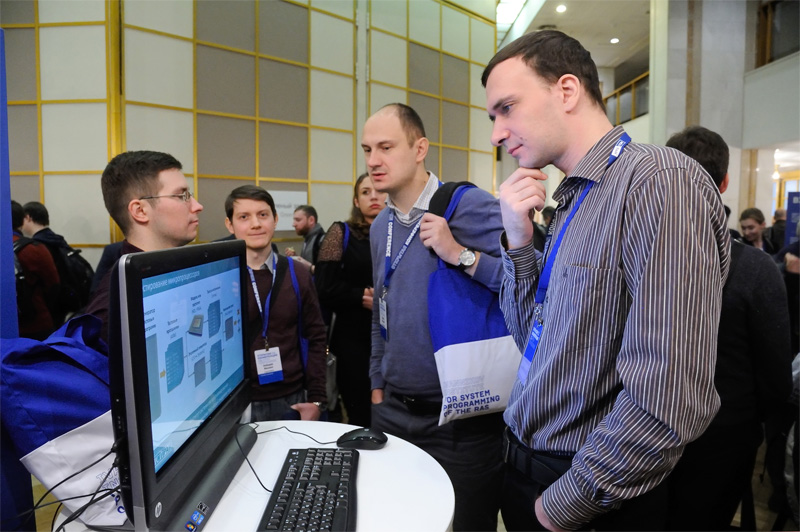
11:30-13:30, Exhibition of technologies (The Green Hall – The Foyer)
Download Catalogue of technologies (PDF)
Svace is an essential tool of the secure software development life cycle, the main static analyzer that is used in Samsung Corp. It detects more than 50 critical error types. Svace supports C, C++, C#, and Java. Svace is registered in the National Software Unified Register, which is kept by the Ministry of Digital Development.
BINSIDE is a tool for detecting flaws in a program using static analysis of executable code.
Anxiety is a framework for detecting errors and potentially dangerous cases in the process of development, acceptance testing and operating the software.
Binary code analysis platform based on QEMU emulator. The ISP RAS platform for program analysis is built on the basis of an open QEMU emulator, which is used when crossplatform development is needed.
ISP Obfuscator is a set of technologies to prevent mass exploitation of vulnerabilities resulting from errors or bookmarks. If the hacker is able to attack one of the devices with the common software, the rest will remain protected by changes made to the code.
Protosphere is a system of deep packet inspection (DPI). It is the part of intrusions and information leaks protection. Detects inconsistencies between protocol specification and specific implementation. Allows you to quickly add support for new (including closed) protocols due to the flexibility of the internal representation.
Klever is a static verification system that uses advanced tools to thoroughly check the security, reliability and performance of software systems developed in the GNU C language. In particular, it is used to verify the real-time OS.
MicroTESK is a reconfigurable and expandable test program generation environment for functional microprocessors verification. It allows automatically constructing test program generators for target microprocessor architectures based on their formal specifications. MicroTESK is applicable for a wide range of architectures (RISC, CISC, VLIW, DSP).
Retrascope is a tool for reverse engineering and functional verification of digital equipment descriptions. It provides automated tools for extracting and analyzing formal source code models. The tool supports synthesized subsets of Verilog and VHDL languages.
AstraVer Toolset is a system for deductive verification of key components. It allows developing and verifying security policy models, as well as providing evidence of the correctness of key components in C language. The necessary tool to achieve the goals of the ADV_SPM and ADV_FSP trust families defined in GOST R ISO / IEC 15408-3-2013.
MASIW is a set of tools for developing software and hardware packages for mission-critical systems in the field of aviation, medicine, and others. It is created for design engineers of aircraft on-board equipment developed using integrated modular avionics (IMA). It quickly adapts to other subject areas.
Constructivity 4D is a technology for creating ambitious software systems and services operating with large arrays of spatio-temporal data and dynamic scenes. It is able to conduct a visual analysis of millions of objects with different geometric representations and individual dynamic behavior. The technology is implemented in the Synchro system, designed for 4D-modeling of large industrial sites.
Texterra is a scalable platform for extracting semantics from text. It is the basic set of technologies for creating multifunctional applications. It analyzes texts using concept identification. It is included in the Unified Register of Russian software.
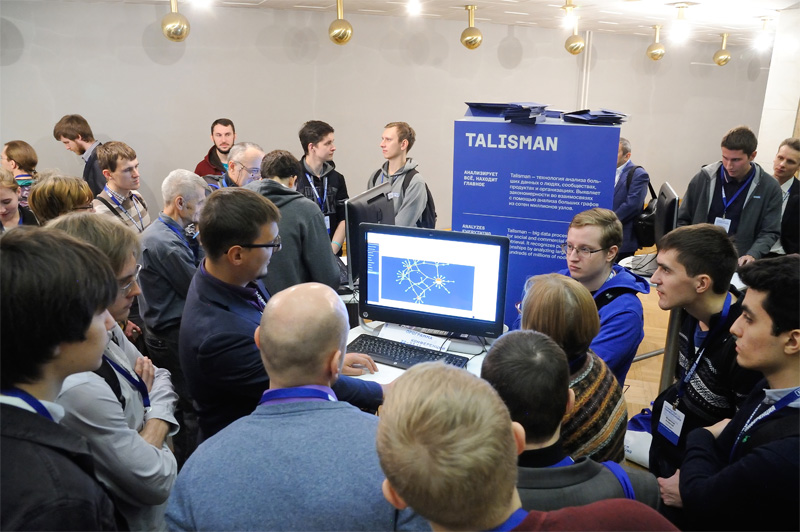
Talisman – big data processing solution for social and commercial information retrieval. It recognizes patterns in relationships by analyzing large graphs from hundreds of millions of nodes.
Lingvodoc is a system intended for collaborative multi-user documentation of endangered languages, creating multi-layered dictionaries and performing scientific work with the received sound and text data. Joint project with the Institute of Linguistics of the Russian Academy of Sciences and Tomsk State University. Under development since 2012. Project website – lingvodoc.ispras.ru.
SciNoon is a system for researcher’s inquiry of scientific articles. Combines a number of unique features to optimize the process of searching and analyzing the results. It particularly allows you to work in a team and keep a history of user actions. Can work with big data.
Complex of solutions for creating service-oriented data processing center provides the ability to store data and perform complex, resource-intensive calculations using both containers and virtual machines. It is particularly intended for the deployment of cloud environments.
Friday, 23 November
Registration. Welcome coffee (The Green Hall – The Foyer)
Blockchain Technology
Nikolay Pakulin1
1 Pax Datatech, Seoul, South Korea
"Challenges and advances of blockchain technologies"
Download PDF
Evgeniy Shishkin1
1 InfoTeCS
"Verifying functional properties of smart contracts using symbolic model-checking"
Aleksandr Kormiltsyn1, Chibuzor Udokwu1, Kondwani Thangalimodzi1, Alex Norta1
1 Tallinn University of Technology
"An Exploration of Blockchain-Enabled Smart-Contract Applications in the Organization"
Learn moreDownload PDF
Coffee, tea
Alexandr Andryukhin1
1 KCD LLC
"Phishing Attacks and Preventions in Blockchain Based Projects"
Learn moreDownload PDF
Andrey Demichev1, Alexander Kryukov1, Nikolai Prikhod’ko2
1 Skobeltsyn Institute of Nuclear Physics, Lomonosov Moscow State University, 2 Yaroslav-the-Wise Novgorod State University
"The Approach to Managing Provenance Metadata and Data Access Rights in Distributed Storage using the Hyperledger Blockchain Platform"
Learn moreDownload PDF
Ilya Evdokimov1
1 Dexpa LLC
"Distributed Infrastructure for B2B Loyalty Programs on Top of the Tendermint Protocol"
Learn moreM. Levin1
1 Pax Datatech
"Tail chain — a new generation blockchain for parallel transaction processing"
Download PDF
Open source software in continuum mechanics problems solving
Corresponding Member of RAS, Prof., Dr. Sci. (Phys.-Math.) Yuri Vassilevski1,2,3
1 Marchuk Institute of Numerical Mathematics RAS, 2 Moscow Institute of Physics and Technology, 3 Sechenov University
"Personalized mathematical models of blood flows"
Download PDF
Olga Sorokovikova1, Dmitry Dzama1, Danil Asfandiyarov1
1 The Nuclear Safety Institute (IBRAE)
"Specialized robust CFD RANS microscale meteorological model for modelling atmospheric processes and contamination transport in urban and industrial areas"
Learn moreDownload PDF
Andrey Epikhin1, Matvey Kraposhin2
1 BMSTU, 2 ISP RAS
"Numerical simulation of acoustic perturbations induced by low-Reynolds jet flow"
Download PDF
Coffee, tea. Poster session.
Konstantin Belyaev1, Eugene Morozov1, Natalia Tuchkova2, Guriy Mickailov2
1 Shirshov Institute of Oceanology, 2 Dorodnicyn Computing Center FRC CSC RAS
"Estimates of Antarctic bottom water transport by MPI-ESM model with assimilation of observational data"
Learn moreDownload PDF
Andrey Ivantsov1, Tatyana Lyubimova1
1 Institute of continuous media mechanics UB RAS
"Numerical simulations of liquid drop dynamics in porous medium using adaptive mesh"
Learn moreDownload PDF
Lunch
Maxim Khomenko1, Fikret Mirzade1
1 ILIT RAS - Branch of the FSRC "Crystallography and Photonics" of RAS
"Validation of hydrodynamic model of laser cladding based on Openfoam solver"
Learn moreVictor Zhukov1, Nataliya Novikova1, Olga Feodoritova1
1 KIAM RAS
"About numerical modeling of flows in high-speed combustion chamber based on OpenFOAM"
Learn moreKirill Ovchinnikov1
1 State Marine Technical University
"Numerical simulation of motions of ship with moonpool in head waves"
Learn moreDownload PDF
Victoria Korchagova1,2, Sofia Sautkina2, Ivan Fufaev3, Ilia Marchevsky1,2, Vladimir Lukin1,2,3
1 ISP RAS, 2 BMSTU, 3 Keldysh Institute of Applied Mathematics
"On Efficient Implementation of Discontinuous Galerkin Method For Numerical Simulation of Two-Dimensional Gas Dynamic Flows on Unstructured Meshes"
Learn moreYulia Sharova1, Olga Olkhovskaya1, Gennadiy Bagdasarov1, Vladimir Gasilov1
1 Keldysh Institute of Applied Mathematics
"High performance computations for short-lived plasmas"
Learn moreDownload PDF
Coffee, tea
Vladimir Sudakov2, Yuri Nechaev1, Vladimir Osipov2
1 ITMO University, 2 KIAM RAS
"Dynamic NEURO-FUZZY model of traffic control of the transport stream"
Learn moreAlena Chernova1,2, Thomas Raeder1, Valentin Tenenev1, Maria Koroleva1,3
1 Kalashnikov ISTU, 2 JSC "INNTS", 3 UdFRC UB RAS
"Multilevel Simulation of Direct Operated Safety Valve"
Learn moreStepan Rogozin1, Evgeny Ivashko2
1 Petrozavodsk State University, 2 Institute of Applied Mathematical Research KarRC RAS
"The optimization of a residential wood log stove using the BOINC system"
Learn moreArtem Nuriev1
1 Lobachevsky Institute of Mathematics and Mechanics, Kazan federal university
"Identification of the parameters of the aerodynamic influence on the beams performing resonance oscillations in air. Experiment and numerical simulation"
Learn moreTechnologies of program analysis, modeling and transformation (Blue hall)
Ivan Vasilev1
1 Novgorod State University
"OS-agnostic process’ and thread’ identification in virtual machine, to support selective instrumentation"
Download PDF
Alexey Vishnyakov1, Alexey Nurmukhametov1, Shamil Kurmangaleev1, Sergey Gaisaryan1
1 ISP RAS
"Method for analysis of code-reuse attacks"
Learn moreDownload PDF
Andrey Mikhailov1, Alexei Hmelnov1
1 ISDCT SB RAS
"Generation of code for reading data from the declarative file format specifications written in language FlexT"
Learn moreDownload PDF
Vladislav Stepanov1, Pavel Dovgalyuk1, Dmitriy Poletaev1
1 Yaroslav-the-Wise Novgorod State University
"Tracing ext3 file system operations in the emulator QEMU"
Learn moreDownload PDF
Coffee, tea
Sevak Sargsyan1, Shamil Kurmangaleev2, Jivan Hakobyan1, Matevos Mehrabyan1, Seryozha Asryan1
1 Russian-Armenian University, 2 ISP RAS
"Directed Fuzzing Based on Program Dynamic Instrumentation"
Learn moreDownload PDF
D. Kononov1
1 ISP RAS
"Executable code analysis approach based on software architecture recovery"
A.V. Samonov1, G.N. Samonova1
1 Mozhaiskiy Military Space Academy
"Methodology and Tools for Development and Verification of formal fUML Models of Requirements and Architecture for Complex Software and Hardware Systems"
Learn moreDownload PDF
Hayk Aslanyan1
1 ISP RAS
"Platform for interprocedural static analysis of binary code"
Learn moreDownload PDF
Lunch
Fedor Niskov1, Andrey Fedotov1, Shamil Kurmangaleev1
1 ISP RAS
"Crash processing for selection of unique defects"
Learn moreDownload PDF
S.G. Kovalev1
1 Positive Technologies
"Reading the contents of deleted and modified files in virtualization based black-box binary analysis system Drakvuf"
Learn moreDownload PDF
Ilja Zakharov1, Evgeny Novikov1
1 ISP RAS
"Compositional Environment Modelling for Verification of GNU C Programs"
Learn moreDownload PDF
Coffee, tea
11:20-13:20, Poster session (The Green Hall – The Foyer)
Tatiana Stenina1, Tatiana Elizarova2, Matvey Kraposhin3, Daniil Ryazanov1
1 Lomonosov Moscow State University, 2 Keldysh Institute of Applied Mathematics of the RAS, 3 ISP RAS
"Numerical simulation of the heart disk pump using OpenFOAM open-source code platform"
Stanislav Stashevskiy1, Vladimir Zenkin1
1 BMSTU
"Determining the characteristics of the intake channels of reciprocating engines using OpenFOAM"
Alexey Ryakhovskiy1, Valery Antonov1, Alexander Schmidt2
1 SPbPU, 2 The Ioffe Institute
"CFD and DSMC approaches to modeling MHD re-entry flow control in OpenFOAM"
Kseniia Kuzmina1, Ilia Marchevsky1, Evgeniya Ryatina1
1 BMSTU
"On capabilities of the open-source code VM2D for modelling of two-dimensional viscid flows by vortex methods"
Victoria Bondarchuk1, Anastasia Gladkova1, Andrew Popov2
1 BMSTU
"Usage of open-source codes for modelling of viscid incompressible flows by PFEM-2 method"
Kirill Vatutin1, Matvey Kraposhin1, Sergey Dubinskiy2
1 ISP RAS, 2 JSC VNIIZHT
"Numerical simulation of train aerodynamics during entrance to the tunnel"
Andrew Osipov1, Matvey Kraposhin2, Sergey Strizhak2, Yaroslav Sovetnikov3
1 MIPT, 2 ISP RAS, 3 MAI
"Identification of the gas dynamics parameters of shock wave formed during rocket lift-off"
Valeriia Melnikova1, Georgy Shcheglov1, Sergei Strijhak2
1 BMSTU, 2 ISP RAS
"Capabilities of the open-source code Palabos for simulation of the flow past rotating bodies"
Daniil Riazanov1, Matvey Kraposhin1, Eygene Ryabinkin2
1 ISP RAS, 2 NRC Kurchatov Institute
"OpenFOAM High Performance Computing Solver for Simulation of Internal Wave Attractors in Stratified Flows using Regularized Hydrodynamic Equations"
Learn moreEugenia Zorina1, Albina Gizzatullina1
1 FSBEI HE «Kalashnikov Izhevsk State Technical University»
"Calculation of the resistance of the elliptical body with keel"
Mariya Koroleva1, Albina Gizzatullina1, Evgeniya Zorina1, Olga Mishchenkova1
1 FSBEI HE «Kalashnikov Izhevsk State Technical University»
"Modeling the supersonic gas flow over a missile"
Kirill Terekhov1, Igor Konshin1,Yuri Vassilevski1
1 Marchuk Institute of Numerical Mathematics RAS
"INMOST — a software platform for distributed mathematical modelling"
Programme Committee
Steering committee
- Arutyun Avetisyan, Prof., RAS corresponding member, ISP RAS.
- Garbuk S.V., Ph.D., Advanced Research Foundation (ARF).
- Gergel V.P., Prof., NNSU.
- David Alan Grier, 2013 IEEE Computer Society President, George Washington University.
- Zhizhenko A.B., Prof., RAS academician.
- Kalyaev I.A., Prof., RAS academician, RI MCS SFU.
- Hironori Kasahara, IEEE CS President Elect 2018, President 2018, Waseda University.
- Lyutikov V.S., FSTEC Russia.
- Costas Stasopoulos, IEEE Director Region 8, Electricity Authority of Cyprus.
- Fedosov E.A., RAS academician, FGUP GosNIIAS.
- Dennis Tsichritzis, President of the Hellenic Foundation for Research and Innovation (ELIDEK).
Organizing Committee
- Arutyun Avetisyan, Prof., RAS corresponding member, ISP RAS.
- Belousov Igor, Prof., SAP .
- Volkov Dmitry, editor-in-chief ("Open Systems"), senior research fellow (Keldysh Institute of Applied Mathematics).
- Ivanov Sergey, Hewlett Packard Enterprise, Russia.
- Konyagin Dmitriy, NVIDIA.
- Luchinin Nikolay, Dell, Russia.
- Pakulin Nikolay, Ph.D., ISP RAS.
- Prokhorov Sergei, Prof., MIPT.
- Samovarov Oleg, Ph.D., ISP RAS.
Programme Committee
Technologies of program analysis, modeling and transformation
- Arutyun Avetisyan, Prof., RAS corresponding member, ISP RAS.
- Belevantsev Andrey, Dr. Sci., ISP RAS.
- Volkonsky V.Yu., Ph.D., JSC "MCST".
- Gaysaryan Sergey, Ph.D., ISP RAS.
- Devyztin P.N., Prof., ISEDU .
- Drozdov Alexander, Prof., MIPT.
- Kanatov Alexey, Ph.D., Samsung.
- Koverninsky I.V., FGUP GosNIIAS.
- Kuznetsov S.D., Prof., ISP RAS.
- Makarov Vladimir , Ph.D., NovSU.
- Ostanevich Sergey, Intel.
- Petrenko Aleksander, Prof., ISP RAS.
- Proskurin Vadim, Ph.D., EMA IS.
Management of Data and Information Systems
- Denis Turdakov, Ph.D., ISP RAS.
- Natalia Loukachevitch, Dr. Sci., Research Computing Center of Moscow State University.
- Dmitry Ustalov, Ph.D., University of Mannheim.
- Kuznetsov Sergey, Dr. Sci., Professor, ISP RAS.
- Anton Korshunov, Ph.D., Quantum.uk.
- Nikita Astrakhantsev, Ph.D., Microsoft Corp.
- Dmitry Lizorkin, Ph.D., Google LLC.
- Boris Dobrov, Ph.D., Research Computing Center of Moscow State University.
- Elena Tutubalina, Ph.D., Kazan Federal University.
- Andrei Tchernykh, Dr. Sci., Prof., CICESE Research Centre (Ensenada, Baja California, Mexico).
- Oleg Samovarov, Ph.D., ISP RAS.
- Andrey Filchenkov, Ph.D., ITMO University.
- Nikolai Kuzjurin, Dr. Sci., Prof., ISP RAS.
- Vasily Velikhov, Ph.D., NRC "Kurchatov Institute".
Open source software in continuum mechanics problems solving
- Prof J.M. Redondo, Universitat Politècnica de Catalunya, PELNoT, LAB-ERCOFTAC.
- Kornev N.V., Prof. Dr-Ing. habil., Universitat Rostock.
- Dr. Henrik Rusche, WIKKI Gesellschaft fur numerische Kontinuumsmechanik mbH.
- Chashechkin Yu D.,Prof., Ishlinsky Institute for Problems in Mechanics RAS.
- Tkachenko I.V., Prof., SPbMTU.
- Yakobovsky M.V., RAS corresponding member, Prof., Keldysh Institute of Applied Mathematics.
- Scheglov G.A., Prof., Bauman MSTU.
- Strizhak S.V., Ph.D., HP, ISP RAS.
- Sigbatullin I.N., Ph.D., Department of Mechanics and Mathematics, Lomonosov Moscow State University.
- Marchevskiy I.K., Ph.D., Bauman MSTU.
- Kraposhin M.V., ISP RAS.
- Terekhov K.M., Ph.D., INM RAS.
- Artem Nuriev, PhD, Lobachevsky Institute of Mathematics and Mechanics, Kazan federal university.
- Banholzer M., Universität der Bundeswehr München.
- Traxinger C., Universität der Bundeswehr München
Reviewers
We express gratitude to everyone who participated in reviewing the publications for the Conference.
From ISP RAS
Oleg Samovarov, Alexander Petrenko, Alexander Gerasimov, Alexey Khoroshilov, Andrey Belevantsev, Denis Turdakov, Shamil Kurmangaleev, Dmitriy Melnik, Nikolay Kuzyurin, Matvey Kraposhin, Sergey Strizhak, Sergey Kuznetsov, Vartan Padaryan, Ivan Andrianov, Konstantin Arkhipenko, Maxim Bakulin, Kirill Batuzov, Oleg Borisenko, Ruben Buchatskiy, Maxim Varlamov, Alexander Getman, Andrey Gomzin, Ksenia Dolgorukova, Mikhail Drobyshevsky, Mikhail Ermakov, Roman Zhuikov, Vladislav Ivanishin, Victoria Korchagova, Leonid Kruglov, Arina Kryuchkova, Victor Kulyamin, Alexey Laguta, Vladimir Mayorov, Mikhail Mandrykin, Ivan Mashonskiy, Alexander Monakov, Yaroslav Nedumov, Sergey Panasenko, Daniil Ryazanov, Kirill Skornyakov, Elena Smirnova, Mikhail Solovyov, Evgeniy Sharygin, Igor Bogomolov, Valeriy Ignatiev, Evgeniy Karpulevitch, Maxim Mishechkin, Roman Pastukhov, Maxim Ryndin, Vyacheslav Stroev, Andrey Sysoev, Andrey Tapekhin, Yulia Trofimovitch, Alexander Yatskov, Vadim Kaushan, Andrey Epihin, Andrey Ryzhov, Nikolay Pakulin, Mikhail Levin, Konstantin Koshelev.
From other scientific organizations
- Andrey Kuleshov (Keldysh Institute of Applied Mathematics, RAS)
- Tatiana Elizarova (Keldysh Institute of Applied Mathematics, RAS)
- Dmitriy Isaev (Higher School of Economics, Moscow)
- Vasiliy Kramarenko (Moscow Institute of Physics and Technology, Institute of Numerical Mathematics, RAS)
- Natalia Dimitrieva (Institute of Hydromechanics, National Academy of Sciences of Ukraine)
- Georgiy Shcheglov (Bauman Moscow State Technical University)
- Ilya Marchevskiy (Bauman Moscow State Technical University)
- Artem Nuriev (Lobachevsky Institute of Mathematics and Mechanics, Kazan federal university)
- Elena Tutubalina (Kazan federal university)
- Boris Dobrov (Research Computing Center, Lomonosov Moscow State University)
- Ilias Sibgatullin (Lomonosov Moscow State University)
- Dmitriy Manushin (Lomonosov Moscow State University)
- Vladimir Makarov (Novgorod State University)
- Victoria Salamatova (Sechenov University)
- Andrey Filtchenkov (ITMO University)
- Anton Korshunov (Quantum.uk)
- Nikita Astrakhantsev (Microsoft Corp.)
- Natalia Lukashevitch (Research Computing Center Lomonosov Moscow State University)
- Kirill Terekhov (Stanford University)
- Dmitriy Ustalov (University of Mannheim)
- Andrey Tchernyh (the Center for Scientific Research and Higher Education at Ensenada, Mexico)
- Ahmad Al-Zoubi (Institute of Thermal Engineering, Technische Universität Bergakademie Freiberg)
- Jörn Beilke (Ingenieurbüro Dr. Beilke)
- Matthias Banholzer (Universität der Bundeswehr München)
- Christoph Traxinger (Bundeswehr University Munich)
Registration
Paticipation in the conference and publication of articles are free of charge. Travel and accommodation, as well as other expenses are to be paid by the participant.
To participate for this conference, please contact the Registration staff at the e-mail address isprasopen@ispras.ru to get instructions.
Submission
We solicit original and unpublished articles of current research, results or work in progress. We invite both researchers and practitioners to submit early research work or general discussions. All accepted papers will be published in the Proceedings of Ivannikov ISP RAS Open Conference.
The papers should be 3 to 7 pages long, formatted using IEEE Manuscript Templates for Conference Proceedings. The proceedings will be published online in IEEE Xplore digital library. Peer review is double-blind. Please remove any references to authors, such as names, affiliations or emails, from submitted manuscripts, as well as direct references to previous work. In the case of successful review and acceptance you will be requested to submit camera-redy text with necessary author details.
Articles submission due to September 19, 2018 September 5, 2018.
Submission is open at EasyChair.
Organizing and Program Committees of Ivannikov ISP RAS Open Conference look forward for cooperation with authors to ensure a process that is both fair in practice and perceived to be fair by everyone.
Submissions that violate these guidelines will be rejected.
Venue Information
Where to find us
Location
The conference takes place at the Main building of the Russian Academy of Science. See the map for exact information.
Transport
To get to the venue place, you can take one of the city bus lines or railways Moscow Metro. All the services are comfortable to reach into the place.
Hotels
Suitable Hotels and Restaurants are surrounded all the area. Here you will find our recommendations.